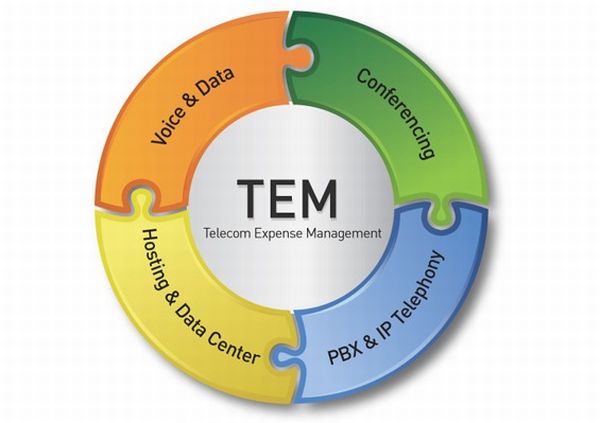
What is Telecom Expense Management (TEM)?
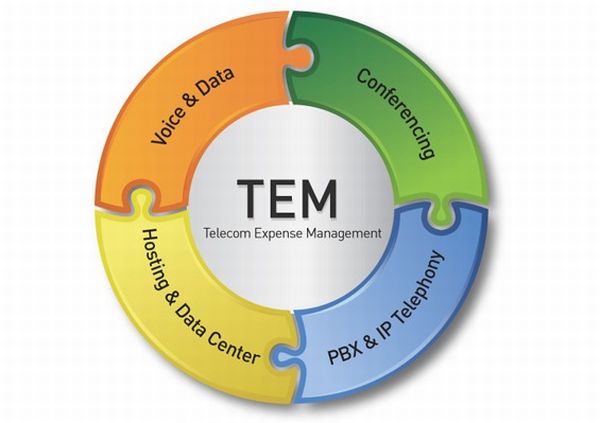
Telecommunications Expense Management (TEM) is the methodology by which organizations can best manage one of their most critical strategic assets: the telecom network.
TEM encompasses the technology, processes, policy, and people needed.
On the technology side, there needs to be a software platform to help inventory your Telecom assets (e.g., circuits, services, equipment, locations, invoices, accounts), enforce business processes (e.g., ordering, approving, problem resolution), and manage access to critical Telecommunications infrastructure information.
The processes are all the business rules, which govern how the network will be deployed, managed, and eventually dismantled or converted.
The policy is the corporate buy in and ultimately the enforcement of the processes that will ensure the integrity of the TEM solution.
The people are the experts in networking and telecom that follow the methodologies and use the software to deploy, manage, and decommission the telecom network.

Things You Can Do With TEM
Once you have all the technology, processes, policy, and people in place in your telecom organization, what types of things will you be able to do to better manage your telecom operations? The following is a sample list of some of these things:
- Maintain a complete an accurate inventory of every network element in your company including every circuit, service, computer, blackberry, cellphone, hub, server, wiring panel, laptop, PDA, etc.
- Just in time provisioning — order what you need when you need it
- Convert from technology to technology easily
- Assess the impact of the network on the company’s bottom line
- Pay your bills on time
- Validate the accuracy of your invoices
- Allocate costs back to the appropriate organization
- Allocate usage of the network back to the organizations that consumed the bandwidth
- Dispute invoice charges with the carrier
- Predict future network costs
- Build your telecom budget
- Identify weaknesses in your security infrastructure
- Optimize your existing network infrastructure
- Electronically bond with your service providers
- Understand the true costs of operating the network
- Negotiate better contracts with your providers
- Measure your SLAs internally and externally
- Analyze your Call Detail Reporting (CDR) from your invoices and your telephone switches
- Centralize all your telecom data into one single repository for doing data reporting, analysis, and business intelligence.

The TEM Disciplines
There are many disciplines that are required to deploy a fully function TEM initiative.
Inventory Management
The center of the TEM universe is the inventory. It goes without saying that you can’t manage what you don’t know exists. It is critical for large enterprises to have a central repository of every circuit, service, router, PBX , cell phone, order, invoice, card, computer, monitor, etc. It is also critical for the organization to know how that inventory is configured, what its purpose for existing is, and how it is related to all the other inventory elements.
Order Management
Once you have an inventory, it is critical to keep it accurate. The way to do this is put in place a best practice repeatable process to put items into the inventory, change those items, and eventually remove those items from inventory. Technology can really help in this area by providing software-based workflow engines to enforce the company rules for how these inventory updates happen. Not only will these processes ensure the accuracy of the inventory, but they will also provide a ton of business intelligence regarding the process…how it works, how it breaks down, who is fast, who is slow, how long does it take, etc?
Financial Management
Financial Management deals with the dollars and cents portion of operating the network and allocating the cost of the network back to the various users in the corporation. The simplest form of Financial Management is paying the bills for the purchase/lease of various network assets. Part of this process is to validate that what is being billed is actually what is being used. In the telecom portion of the TEM space, this means checking each line item from invoices and comparing them to the inventory. Another part of this process is validating that the amount being billed is accurate and this is accomplished by checking the detailed elements of the bill against the configuration of the telecom service, the tariff and the contract on a monthly basis.
It is a well-known fact that corporations are spending at least 10% more on their telecom bills than they should due to the lack of decent technology and processes internally to manage their telecom invoices. This makes the Financial Management discipline of TEM one area that can lead to some of the hardest ROI dollars for a company implementing TEM. Most companies could easily payback the cost of a TEM initiative within six months to a year by reducing their telecom expenses by 10%+.
The next part of Financial Management involves allocation of costs. Once bills are paid accurately, the next piece is to allocate those charges fairly to the users within the organizations. Allocation can be straightforward in some scenarios. For example, the allocation of a cell phone monthly charge is a simple matter of taking the entire monthly charge for that phone and charging it back to the organization of the person that uses the phone. In the case of charge back of network utilization, this can be much more problematic. In this case, your TEM solution needs to have access to network utilization information that can be used to determine how much of a circuit is used for what purposes. This example is one of the most advanced examples of TEM allocation; however, it is an area that many Telecom Managers should be looking at implementing over the years to come.
Contract Management
Contracts contain the terms and conditions of the customer’s relationship with their carriers. It is critical to manage these contracts as you would manage any of your corporate contracts. You need to ensure that the terms and conditions are met by both parties. The most obvious entity to manage as part of your contract is your price. You need to make sure you are being billed the correct amount of money on your contract. You also need to negotiate your contracts on a regular basis to ensure that you are paying the best rates available in the industry at that time. Finally, you will want to manage your annual commitments, and your Service Level agreements.
Business Intelligence/Reporting
It is one thing to maintain an inventory, pay bills or put processes in place to ensure accuracy. It is totally another to take all the data that is generated from following the TEM processes, and analyze the data for the company’s benefit. This is the role of Business Intelligence in TEM. You need to harness the value of your data to budget and forecast your telecom spend, perform “What If” analysis on network conversions or contractual terms, or simply distribute out pertinent performance data about the telecom network and its cost to all the consumers of those services that are paying for them. Business Intelligence can also be used to measure the performance of your telecom network by using Key Performance Indicators (KPI) that will automatically alert managers when certain thresholds have been exceeded.
Network Management
The next piece of the TEM puzzle is the tie-in to network management systems. This is the management phase of the inventory life cycle. On a day to day basis, assets break, change, etc. The only way network management systems can monitor the network is to know what is out there, how it used, who uses it, etc. This goes back to importance of the inventory. Network management can only be as good as the inventory. In the network centric world that corporate America is transforming into, it is critical to keep all network assets working 24 hours. A single $500 circuit going down can cause multi-million dollar losses for a company.
Incident Management
Network Management systems identify potentially issues that require resolution from various organizations. Incident Management logs the issue, and gets the problem into the hands of the correct person to resolve the problem. Once again, the inventory plays a critical role in providing the correct information to the person trying to resolve the problem. The ordering information can play a huge role as well in case some changes were recently logged on a particular piece of inventory that might account for the incident happening in the first place. Another side benefit of Incident Management is that organizations need to measure their service level agreements to see how well the network is performing. These service levels could be internally (for Ethernets that might go down or slow down at certain times each day) or they could be externally with Service Providers such as telephone companies, wiring companies, equipment installation crews, etc.
Design and Optimization
Telecom design is a very mature craft to seasoned telecom professionals. TEM can leverage all the information in the database to help your engineers design the highest performing network… hopefully for the most economical price. TEM will also provide timely information to provisioning staff as to when capacity needs to be upgraded or downgraded. This is called “Just in Time Provisioning.” TEM will also be used to design future network architectures supporting applications like VoIP or video that require inputs from multiple sources. Capacity Management is another aspect of TEM. It is critical to manage the your network elements as well as over and under-subscription levels on MPLS, IP and Wireless networks.
Security Management
Security has been a growing concern over the last decade and it will continue to be so as more wireless access is happening. Tying this back to the other segments of TEM, you can’t do great security management unless you know every device plugged into the network, what software it is running, when it was installed, who uses the device… back to the importance of the inventory. The installation process is critical as a repeatable process to ensure that all devices plugged into the network get installed in the same way every time… verifying the correct security patches, turning off the correct ports, making sure the passwords are complicated enough… Wireless throws another wrinkle into the equation as now devices can just appear on the wireless network. How will people know if these devices are allowed to connect?